Multi-Factor Authentication (MFA)
Use the authentication providers you're already familiar with to start using MFA with Micetro
Jun 23rd, 2022
With the latest release of Micetro 10.3, we announced the ability to start using Multi-Factor Authentication (MFA) to login in to Micetro through either Azure AD or Okta. Now, you can use Azure or Okta to provide another way to login with SSO (Single Sign-On) or take it a step further and configure MFA using one of these two providers.
What is MFA?
MFA is a security measure which requires that users verify their identity through two or more methods, such as by using a password and some kind of smart card, or more commonly now a password and an authentication app on a phone. There are three main factors of authentication known throughout the security world:
- Something you know (like a password)
- Something you have (like a key card)
- Something you are (like a fingerprint)
Using a mixture of these is often the most secure way to allow access to an app or service.
Why Use MFA?
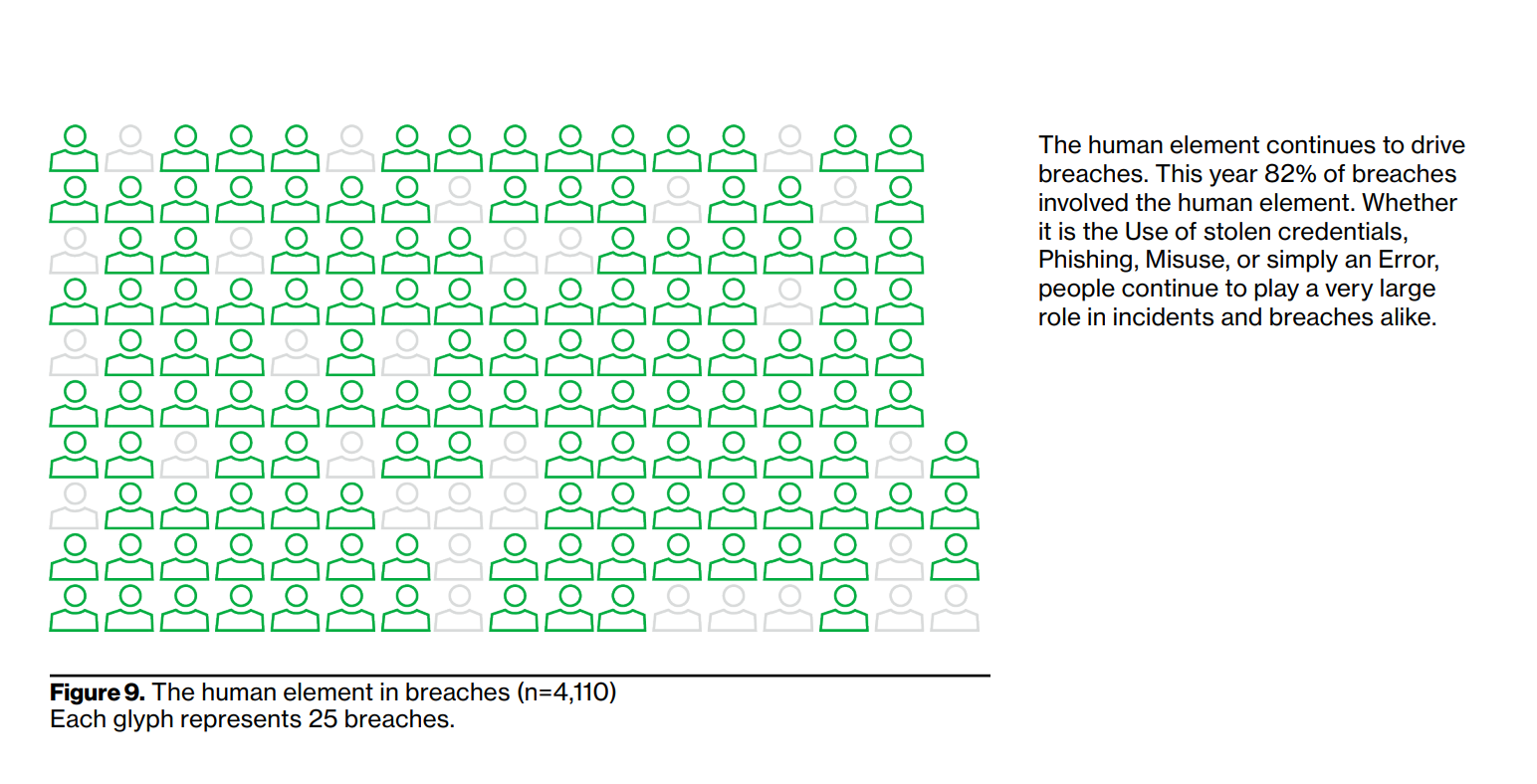
In the 2022 Data Breach Investigation Report by Verizon, it's noted that "the human element continues to drive breaches." In fact, about 82% of attacks were because of human error.
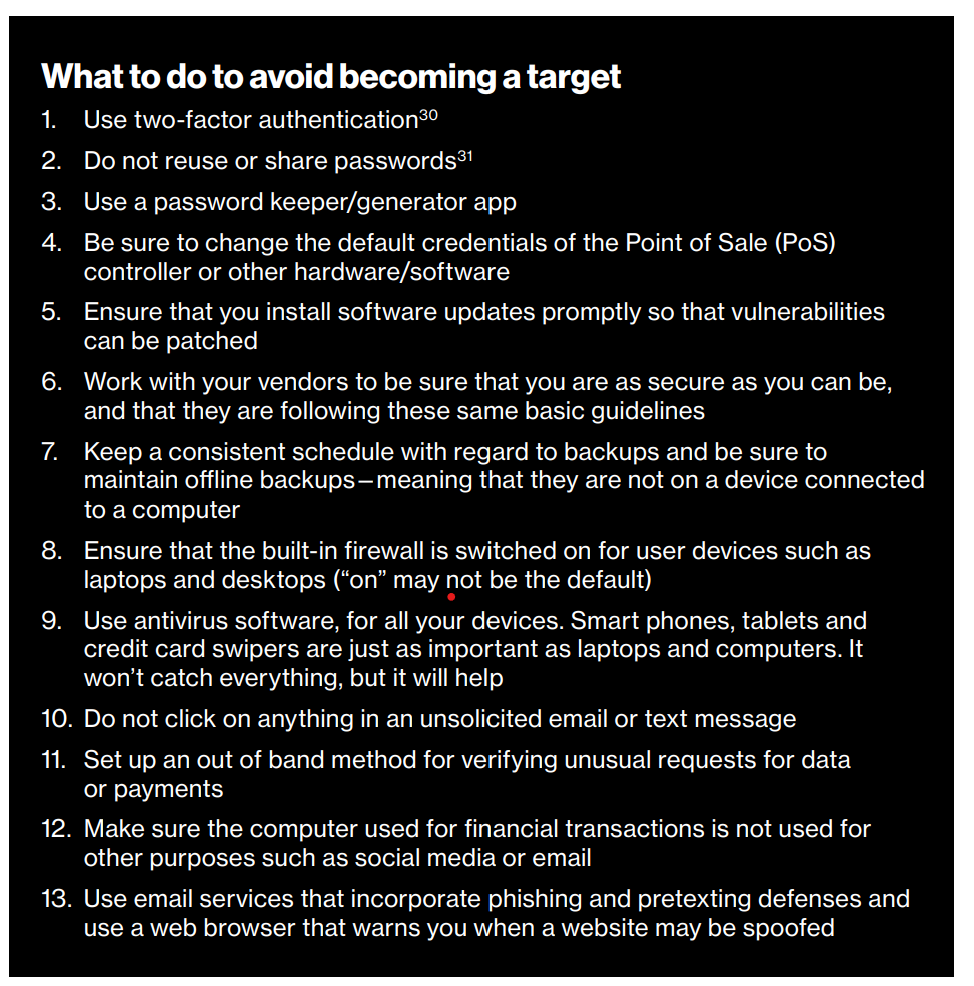
The top security method listed to avoid becoming a target of malicious attacks is to "Use two-factor authentication."
MFA can help combat against attacks which happen due to weak passwords, stolen passwords, phishing scams, and other common social hacks. While MFA isn't new, it's not as inconvenient as it once was. One of the easiest implementations is to have users download either the Microsoft or Google Authenticator app. These apps will provide a one-time password (often called OTP) or provide a push notification with an "Approve" button as a second factor to a typical username/password combination.
MFA and Compliance
Several industries and compliance regulations standards prioritize or even require MFA to achieve compliance. Industries like government, healthcare, and finance can require all of their solutions and partners to use MFA to login to services. Compliance standards like Sarbanes-Oxley (SOX), Health Insurance Portability and Accountability (HIPAA), Defense Federal Acquisition Regulation Supplement (DFARS), and Payment Card Industry Data Security Standard (PCI DSS) in many cases require the use of MFA using at least two out of the three factors listed above (something you know, something you are, or something you have).
Authentication Vendor Considerations
Micetro is in the business of DDI management, so we didn't see any reason to reinvent the wheel and require our customers to introduce yet another security tool to their environments. Our product managers did a careful analysis of the external authentication vendors most businesses were already using.
With a market share of almost 40% and a spot in the leader section of the Gartner Magic Quadrant, Okta was an easy choice. We also kept in mind our close partnership with Microsoft and the amount of customers who are already using Azure to do authentication with Office 365, making Azure another solid choice for authentication support.
Admins can use the following documentation to integrate Micetro with either Okta or Azure. https://docs.menandmice.com/en/latest/guides/implementation/external_auth/?highlight=mfa#multi-factor-authentication
This integration will simply set up the authentication through an external source, much like you may have done for Active Directory to configure SSO. The MFA setup will actually be done within the configuration of either Okta or Azure, depending on which you choose to use.
Because the configuration is done through these vendors, troubleshooting support beyond basic configuration will also be done through Okta or Microsoft to ensure your environment maintains the most secure state possible.
Keeping Your DDI Environment Up and Secure
We understand that security is a top priority for you and that's why we are always improving the ways we help you stay confident and secure. Here are just a few more security capabilities to look out for in your DDI solutions:
- Micetro is a pure role-based access control solution, offering you granular access down to the DNS zone or DHCP scope.
- xDNS (multi-vendor) Redundancy allows you to ensure 100% DNS uptime in the case of a DDOS attack or other DNS provider outage
- Maintain visibility and control of your DNSSEC zones the same as you would for the rest of your DDI environment
- Protect your email using SPF, DMARC, and DKIM DNS records
- Integration with cloud DNS firewalls and other vendors with security expertise
If you'd like to hear more about how we can help you maintain a secure DDI environment and ensure uptime even when your DNS providers go down, come to our live joint webinar with Paessler on June 30!
Multi factor authentication in Micetro 10.3 - live from #ciscolive https://t.co/sqOpRZeYji
— Men&Mice (@Menandmice) June 16, 2022