Privacy, security, and DNS: DoH & DoT
Digital privacy is increasingly pivotal for customers and businesses alike
Apr 3rd, 2019
In a world where digital privacy, whether due to concerns over surveillance or questionable use of data, is increasingly pivotal for customers and businesses alike, unsecured transmissions are simply not acceptable.
Surely DNS, the most fundamental building block of any network, is all good and set, yes? Well, let’s take a closer look.
DNS: connecting people to machines since 1983
The original standard of DNS dates back to 1983. Since then a lot of DNS queries have ‘passed’ under the (proverbial) network bridges.
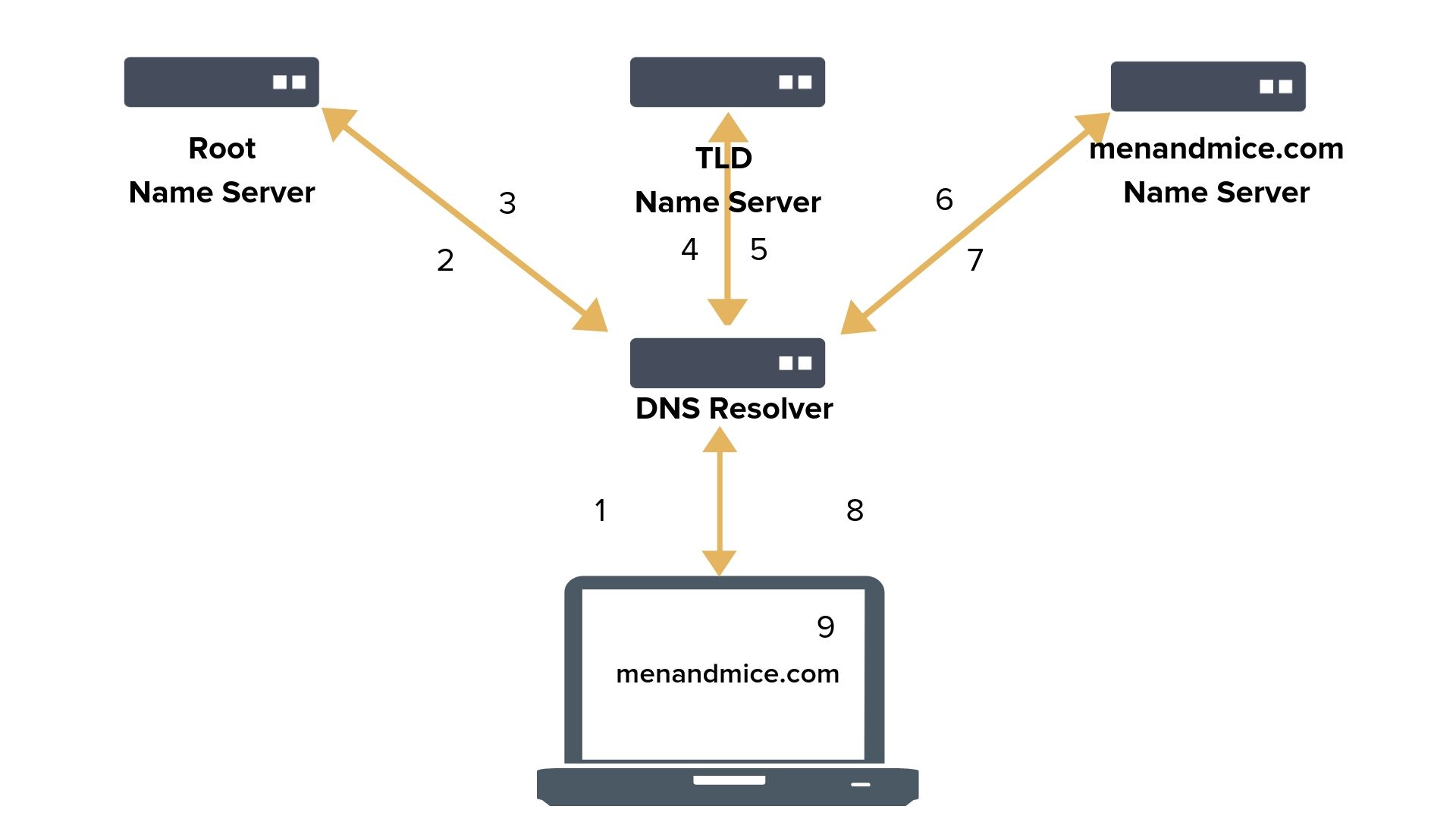
A basic DNS query-response resolution process looks like this:
Spot the problem?
Looking at the communication that’s taking place in resolving even the simplest of DNS queries, there’s a whole lot of action going on -- which can lead to issues in security and privacy. One that stands out almost immediately is that the queries and responses are in cleartext. It’s not hard to imagine a suitable man-in-the-middle attack rerouting the user to a malicious destination.
Early on, DNSSEC was created to prevent such incidents. By establishing a chain of certificates for nameservers, DNSSEC was intended to spread trust across networks.
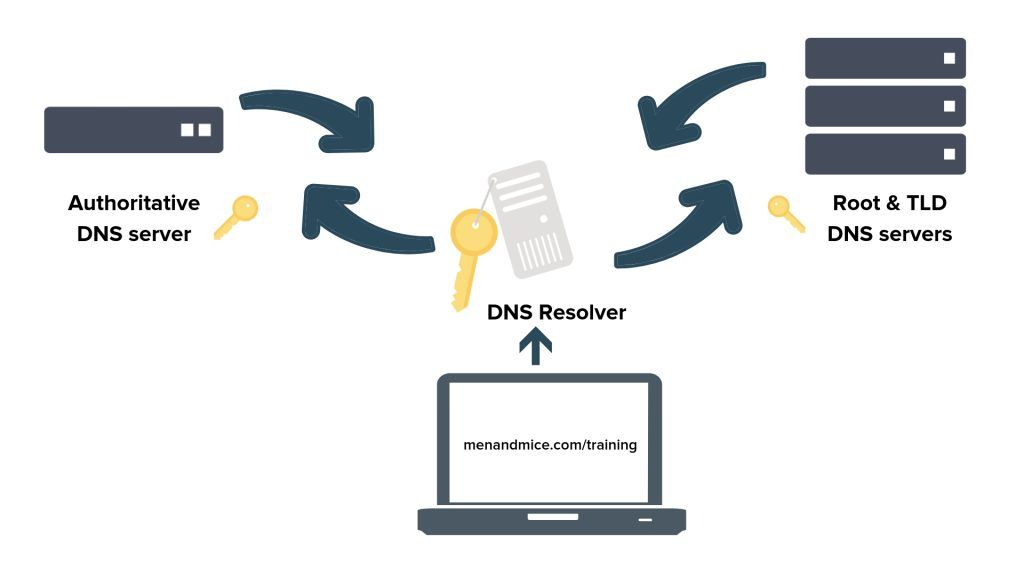
It did not, however, change the fact that the communication is still sent in cleartext. (Also, DNSSEC adoption is about 20% and only about 3% in the Fortune 1000.)
What are we doing to resolve (pun not intended) these issues?
Two ways to secure DNS queries which are currently being explored by, amongst others, the IETF, are doing DNS over TLS or HTTPS.
- DNS-over-TLS (DoT)
The user connects to the DNS resolver through a dedicated port (853). With a strict DoT it will not use any other connection, while when using an opportunistic DoT, it will take the secure port if offered, but if not, it will connect unsecured anyway.
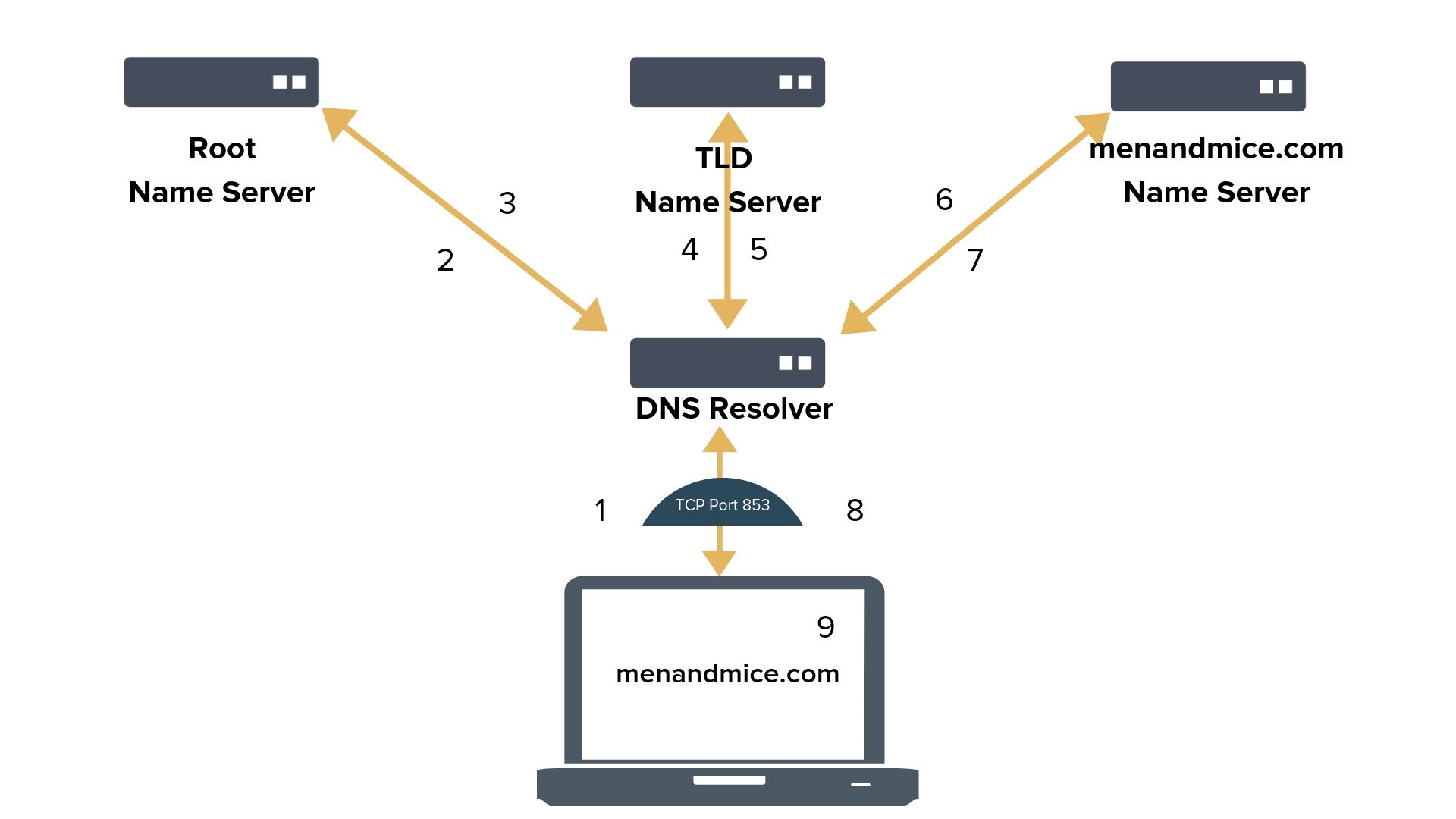
The main weakness of DoT is its limits: it only addresses encryption on a system resolver level and works only on one port. Target the traffic between the resolver and the nameservers or block the port and DoT is over. It can also break split horizon DNS and spawn Server Name Indication (SNI) leaks. (TLS 1.3, however, proposes encrypted SNI.)
- DNS-over-HTTPS (DoH)
With DoH, web applications access DNS using existing browser APIs and DNS traffic is mixed in with regular HTTPS traffic.
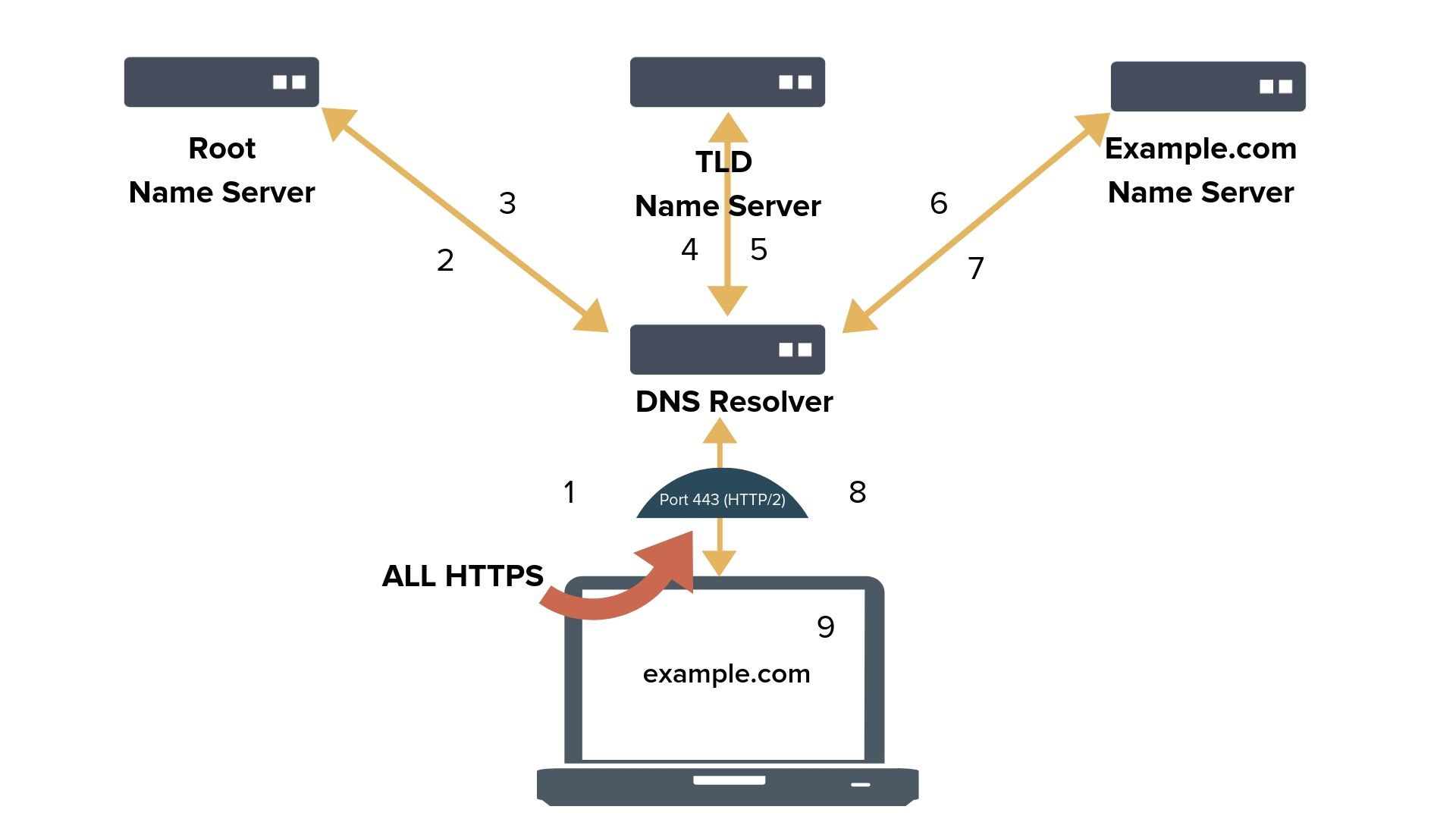
The major challenge for DoH is adoption. Beyond manufacturing latency, it makes securing DNS less transparent and manageable: organizations need to solve new challenges.
YOU get a secure DNS, and YOU get a secure DNS, and…
There’s no one protocol to rule them all, nor is there a need for only one. (Although the number of protocols involved with networks can be seen as daunting -there are 8571 RFCs as of this writing.)
To make a long story short, both DoT and DoH aim to make networks safer. As such, both have their advocates, divided fairly logically by the context in which they work best:
- on-prem private networks are generally more likely to support DoT; not surprisingly, as it provides more control and visibility that’s suited to a limited (however large) network context.
- those developing cloud-based networking solutions, on the other hand, gravitate toward DoH; they can make their applications more efficient by leveraging the existing HTTPS ecosystem and pioneer new technologies like Server Push or resolveless DNS.
Both have their strengths to emphasize and their weaknesses to address.
Where do we go from here?
DNS is no small technology, and things tend to go slow. Both DoT and DoH are fairly young technologies. As with any other technology, we simply cannot predict the challenges they’ll invite.
What we can do is evaluate and discuss.
Whether we talk about censorship or protection of society from harmful content, whether it’s the liabilities born from DNS vulnerabilities or the GDPR, there’s much to debate. On the other hand, technology also keeps progressing independent of such discussions, altering the course of the conversation.
One such place for these debates is RIPE. Men&Mice will be at RIPE 78 in Reykjavik 20-24th May, joining ISPs and other network operators to discuss the future of networks. (And, of course, to change the way the world sees networks.)
In the meantime, you can follow our blog and social media in the coming weeks to learn more about DoT, DoH, and other ways to secure your networks, and join the conversation.